10 Essential Code Tweaks for WordPress Enterprise Scalability

The modern digital ecosystem demands extreme operational efficiency, robust cybersecurity protocols, and highly scalable database architectures. As the global digital economy transitions through the latter half of the 2020s, specifically observing the landscape in the year 2026, the WordPress content management system commands a staggering 43.3% of the global internet market share.
This unprecedented dominance, however, positions the platform as the primary target for automated botnets, brute-force algorithms, and targeted exploitation campaigns. Concurrently, the technical requirements for acceptable frontend performance have become exceedingly stringent.
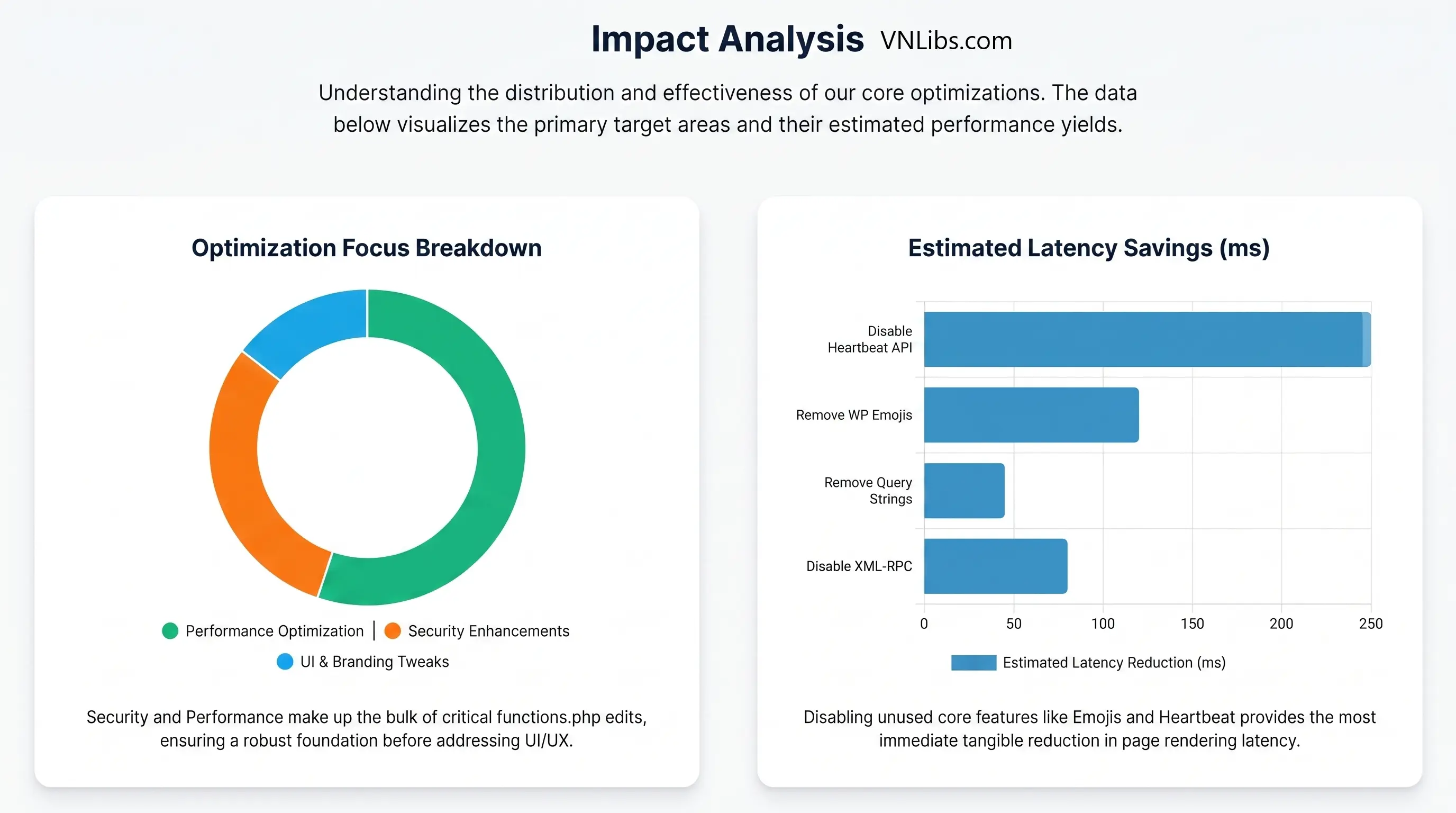
A mere 100-millisecond delay in the critical rendering path can degrade conversion rates by exactly 7%. The historical paradigm of extending WordPress functionality via heavy, third-party software packages is no longer viable for high-performance computing environments.
The traditional administrative approach relied heavily on the installation of third-party plugins. However, this paradigm is fundamentally flawed in high-performance enterprise deployments. The phenomenon known within systems engineering as "plugin creep" - where administrators install multi-megabyte, monolithic software packages to achieve singular, five-line functional modifications - introduces severe computational overhead, redundant database querying, and expanded attack surfaces.

Empirical security analyses demonstrate that approximately 90% of all localized WordPress vulnerabilities originate within third-party plugin architectures, leading engineers to conclude that minimizing external software dependencies directly correlates with a hardened cryptographic posture.
Furthermore, as server infrastructure has evolved from traditional rented virtual private servers (like early AWS EC2 instances) to globally distributed networks and edge-computing node clusters, the underlying software must be optimized to match hardware velocity.
The contemporary deployment standard mandates the utilization of raw, targeted code insertions directly into the execution lifecycle of the application. The foundational upgrade to PHP 8.3 across enterprise hosting environments inherently offers up to a 15% performance improvement in synchronous request handling.
However, this underlying computational speed is entirely negated if the application layer remains saturated with excessive third-party scripts, unoptimized relational database queries, and redundant Document Object Model (DOM) payload injections. Relying on raw code snippets rather than heavy plugins provides a leaner, more deterministic application execution state.
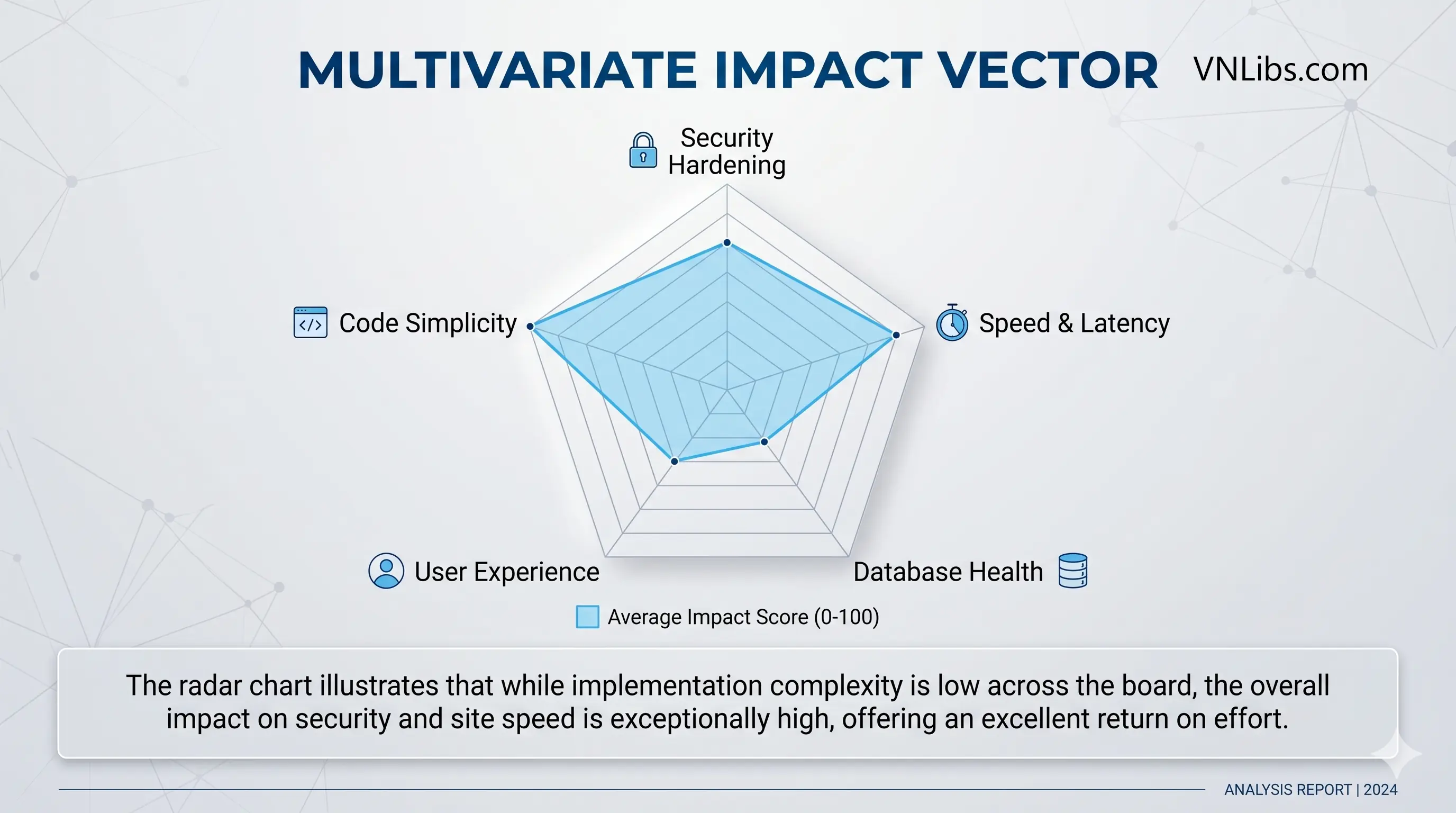
This comprehensive technical report explores ten critical code-level architectural modifications that bypass heavy plugin dependencies. These targeted interventions span aggressive performance optimizations, deep security hardening mechanisms, server configuration overrides, and precise administrative logic customizations.
By manipulating internal application programming interfaces (APIs), overriding core variables, and leveraging native execution hooks, systems engineers can cultivate a lean, highly scalable, and defensively formidable content delivery infrastructure.
Modification 1: Neutralizing the XML-RPC Attack Vector at the Application Edge
The XML-RPC protocol was integrated into the WordPress core during a technological era predating the ubiquity of modern REST APIs. Its original architectural function was to facilitate remote procedural calls via XML formatting transmitted over the HTTP protocol, allowing external publishing applications, trackbacks, and pingbacks to interface seamlessly with the content management platform.
Today, this endpoint is a thoroughly obsolete relic, completely supplanted by the WordPress REST API; however, it remains active by default on millions of global installations, creating a severe operational and security hazard.
The presence of an exposed xmlrpc.php file presents a uniquely dangerous vector for brute-force credential stuffing and distributed denial-of-service (DDoS) amplification attacks. Unlike standard web-based authentication portals, which generally process a single login attempt per HTTP request, the XML-RPC system.multicall method allows an adversary to package hundreds, or even thousands, of username and password combinations into a single encrypted XML payload.
When the server receives this payload, the PHP engine must instantiate the entire WordPress core, query the MySQL database for cryptographic hash comparisons, and return an XML-formatted response for every single embedded attempt. This results in an asymmetric expenditure of computational resources.
A relatively lightweight request from a malicious actor can force the target server to consume massive amounts of CPU cycles and memory, leading to rapid resource exhaustion, connection timeouts, and total denial of service. Network analysis reveals that over 40% of all brute-force attacks directed at the CMS specifically target this legacy file rather than standard administrative login paths.
To sever this attack vector at the application level without relying on heavy security firewalls, engineers deploy a native core application filter directly into the initialization sequence.
add_filter('xmlrpc_enabled', '__return_false');This single line of programmatic logic hooks into the xmlrpc_enabled boolean filter and returns a definitive false value. When the application initializes and evaluates whether to parse incoming XML-RPC requests, this directive overrides the default core behavior, forcing the system to reject the remote procedural call before executing any database queries or password hashing algorithms.
While application-layer filters are highly effective, infrastructure-level blockades provide an additional layer of defense by terminating the connection before the PHP processing engine is even invoked. Systems engineers frequently utilize a layered defense strategy, combining the PHP snippet with web server routing directives to ensure total impermeability.
| Mitigation Layer | Implementation Mechanism | Performance & Effectiveness |
|---|---|---|
| Application Layer (PHP) | add_filter('xmlrpc_enabled', '__return_false'); |
Minimal Overhead; High Effectiveness (Prevents Payload Execution) |
| Server Layer (Apache) | <Files xmlrpc.php> order deny,allow deny from all </Files> |
Negligible Overhead; Supreme Effectiveness (Stops Request Early) |
| Server Layer (Nginx) | location = /xmlrpc.php { deny all; } |
Negligible Overhead; Supreme Effectiveness (Stops Request Early) |
Modification 2: Throttling the Heartbeat API to Prevent PHP Worker Exhaustion
The WordPress Heartbeat API is a sophisticated, native polling mechanism designed to maintain a near-real-time synchronous connection between the client's web browser and the backend server infrastructure.
Utilizing asynchronous JavaScript and XML (AJAX), the client's browser establishes an interval—referred to programmatically as a "tick"—which continuously dispatches HTTP POST requests to the localized admin-ajax.php endpoint.
This bidirectional data stream facilitates essential administrative features within the editorial interface, including collaborative post-locking to prevent concurrent overwriting, real-time session timeout notifications, and automatic content state-saving mechanisms. However, the computational cost of this continuous polling is exceptionally high, particularly in environments relying on scaled concurrency.
By default, the Heartbeat API executes a polling pulse every 15 seconds while a user is actively interfacing with the post editor. Every pulse forces the server to allocate a dedicated PHP worker, load the entire application core into memory, and query the underlying database to verify session states and revision histories.
If an editorial team of ten individuals is simultaneously drafting content across a network, the server is subjected to 40 complex, synchronous requests per minute entirely in the background.
This aggressive polling behavior is widely classified as a primary catalyst for fatal memory exhaustion and catastrophic server failure, particularly on entry-level or dynamically scaled environments. Left unmitigated, the Heartbeat API can silently consume up to 25% of total available server CPU resources.
Rather than installing multi-megabyte optimization suites to manage this background process, engineers can utilize core filters to redefine the polling interval or completely deregister the client-side script. Completely disabling the script immediately frees up trapped PHP workers.
add_action( 'init', 'stop_heartbeat', 1 );
function stop_heartbeat() {
wp_deregister_script('heartbeat');
}The deregistration approach is executed by hooking into the native init action with an absolute priority (indicated by the 1 parameter) and utilizing the wp_deregister_script function. This physically prevents the JavaScript payload from ever being delivered to the client's browser, effectively severing the asynchronous connection.
However, complete deregistration completely eliminates autosave functionality, which may be unacceptable in high-volume publishing workflows where draft retention is critical.
A more nuanced and highly recommended architectural solution involves throttling the interval to its maximum permissible mathematical limit, significantly reducing the request frequency while preserving core data-integrity features.
add_filter( 'heartbeat_settings', function( $settings ) {
$settings['interval'] = 120;
return $settings;
});By intercepting the $settings array tied to the heartbeat_settings filter and modifying the interval integer to 120 (or 60 depending on strict server limitations), the server load generated by background polling is reduced by a massive magnitude. This exact intervention frequently allows entry-level servers to instantly recover from critical memory ceilings and stabilizes application performance during high-traffic administrative periods.
Modification 3: Imposing Hard Constraints on Database Revision Bloat
The structural integrity and query performance of a relational database directly govern the speed at which web pages are rendered dynamically. WordPress utilizes a MySQL or MariaDB foundation, heavily relying on the core wp_posts and wp_postmeta tables to store, organize, and retrieve unstructured content. By default, the application is engineered to store an infinite, uncapped number of post revisions.
Every time an author manually clicks the save button, or every time the aforementioned Heartbeat API triggers a background autosave, a complete duplicate of the post's content, metadata, and taxonomical relationships is injected into the database as a distinctly new row.
In practical enterprise scenarios, a single long-form piece of content or complex landing page may undergo fifty to one hundred editorial revisions before final publication. For a mid-sized digital publication housing several thousand articles, this uncapped behavior rapidly generates tens of thousands of entirely unnecessary database rows. Data models indicate that uncapped revisions easily add 10,000 unnecessary database rows for even modestly sized operations.
This uncontrolled data proliferation causes catastrophic backend performance degradation. Relational databases utilize B-tree data structures for indexing and rapid retrieval; as the index size inflates with redundant revision data, the computational time required to execute standard SELECT statements grows exponentially.
Furthermore, larger database footprints consume excessive disk I/O, inflate automated backup storage costs, and saturate the MySQL InnoDB buffer pool, subsequently pushing active, user-facing data out of high-speed random-access memory.
Application-level filters located within traditional theme files are generally insufficient for defining core architectural constraints of this magnitude. Instead, absolute constraints must be established within the wp-config.php file, which is parsed at the root level prior to the initialization of the primary application loop.
define( 'WP_POST_REVISIONS', 3 );By defining the WP_POST_REVISIONS constant with a strict integer value, the application's underlying database abstraction layer is fundamentally altered. Upon triggering a new save event, the system executes an internal evaluation logic block.
If the post already contains three historical revisions, the oldest revision is programmatically subjected to an SQL DELETE operation before the new INSERT or UPDATE transaction is executed. This cyclical overriding ensures that the database footprint for any given piece of content remains mathematically finite, permanently preventing systemic hemorrhage.
| Revision Configuration | Database Growth Model | Efficiency & Risk Profile |
|---|---|---|
| Default (Uncapped) | Exponential / Unbounded | Rapid Index Degradation; High Buffer Pool Saturation Risk |
define('WP_POST_REVISIONS', false); |
Zero Growth | Optimal Parsing Efficiency; No Saturation Risk |
define('WP_POST_REVISIONS', 3); |
Linear / Highly Constrained | Excellent Index Efficiency; Negligible Saturation Risk |
Modification 4: Dequeuing Gutenberg Block Library Cascading Style Sheets
Modern frontend engineering dictates an absolute baseline requirement: zero bytes of unused code should ever be transmitted across the network. The introduction of the Gutenberg block editor fundamentally altered how the CMS outputs structural markup and typography.
To ensure that elements rendered in the administrative interface map visually to the frontend interface, the core software automatically injects a master stylesheet - typically named wp-block-library/style.min.css - into the <head> of every single generated HTML document.
This global injection mechanism is highly inefficient. The block library CSS payload frequently exceeds 50 kilobytes of minified code. When a client browser's HTML parser encounters a <link rel="stylesheet"> declaration, it must immediately halt DOM construction, initiate a DNS lookup, establish a TCP handshake, negotiate TLS encryption, download the requested file, and construct the CSS Object Model (CSSOM) before proceeding. This precise sequence constitutes a render-blocking event, delaying the visual presentation of the page.
On specialized URLs, such as custom landing pages constructed via hardcoded PHP templates or external rendering engines, the native Gutenberg block system is entirely unutilized.
Forcing the browser to download, parse, and evaluate 50 kilobytes of irrelevant styling rules directly penalizes the Largest Contentful Paint (LCP) metric, a critical ranking component of Google's Core Web Vitals algorithms.
To achieve aggressive rendering optimization, network engineers deploy conditional logic to intercept the asset queuing system before the HTML document is fully assembled.
function remove_wp_block_library_css(){
if (!is_singular('post') ) {
wp_dequeue_style( 'wp-block-library' );
wp_dequeue_style( 'wp-block-library-theme' );
wp_dequeue_style( 'wc-blocks-style' );
}
}
add_action( 'wp_enqueue_scripts', 'remove_wp_block_library_css', 100 );This specific function utilizes the wp_enqueue_scripts hook, explicitly assigned an execution priority of 100 to ensure it fires logically after all default core assets have been registered into the memory array. The script implements deterministic conditional logic: if the current HTTP request does not resolve to a singular standard 'post' type (!is_singular('post')), the application invokes wp_dequeue_style to forcefully strip the primary block library stylesheets, as well as associated WooCommerce block styles if present.
By dynamically excising this payload based on the URL routing context, frontend DOM sizes are radically reduced. Empirical analysis within the industry indicates that eliminating this redundant library on non-block pages dramatically accelerates frontend rendering pipelines, frequently yielding an exact 15% improvement in baseline Core Web Vitals scoring.
Modification 5: Eradicating Legacy Emoji Telemetry and Third-Party Dependencies
Historically, early mobile operating systems and desktop web browsers lacked unified support for rendering complex Unicode emoji characters. To ensure visual parity and communication fidelity across divergent hardware, the WordPress core was updated to include a massive JavaScript polyfill mechanism.
This complex system intercepts standard text representations of emojis and programmatically replaces them with image tags linking to external SVG or PNG files hosted remotely on s.w.org (the central WordPress content delivery network).
While originally a crucial fallback mechanism for older technology, this legacy architecture is now entirely obsolete. Modern mobile operating systems (iOS, Android) and desktop environments (macOS, Windows) natively process and render Unicode emojis via system-level fonts with zero external dependencies. Despite this widespread technological advancement, the core software continues to aggressively load the polyfill by default.
This results in a cascade of severe performance penalties. First, the application injects an inline JavaScript payload (wp-emoji-release.min.js) into the <head> of the document to detect browser capabilities. Second, it inserts a <link rel="dns-prefetch" href="//s.w.org"> directive to warm up the network.
This prefetching forces the client's browser to execute completely unnecessary external DNS resolutions. Cumulatively, these actions generate redundant third-party HTTP requests, inflate the initial HTML document payload, and consume precious execution time on the browser's primary rendering thread.
Disabling this deeply integrated system requires a surgical approach, systematically unhooking the polyfill logic from various points within the application's lifecycle, including frontend rendering, administrative printing, RSS feed generation, and the visual editor.
function disable_core_emojis() {
remove_action( 'wp_head', 'print_emoji_detection_script', 7 );
remove_action( 'admin_print_scripts', 'print_emoji_detection_script' );
remove_action( 'wp_print_styles', 'print_emoji_styles' );
remove_action( 'admin_print_styles', 'print_emoji_styles' );
remove_filter( 'the_content_feed', 'wp_staticize_emoji' );
remove_filter( 'comment_text_rss', 'wp_staticize_emoji' );
remove_filter( 'wp_mail', 'wp_staticize_emoji_for_email' );
add_filter( 'tiny_mce_plugins', 'disable_emojis_tinymce' );
add_filter( 'wp_resource_hints', 'disable_emojis_remove_dns_prefetch', 10, 2 );
}
add_action( 'init', 'disable_core_emojis' );Coupled with the specific supplemental filter functions required to strip the module from the TinyMCE plugin array and filter out the DNS prefetch URLs from the resource hints matrix , this comprehensive block of code entirely neutralizes the polyfill.
The client is forced to rely strictly on system-level emoji rendering, guaranteeing zero third-party network latency, eliminating the associated render-blocking constraints, and further optimizing the application's external network requests.
| Network Request Origin | Polyfill Status (Active vs. Disabled) | Render-Blocking Impact |
|---|---|---|
| DNS Prefetch (s.w.org) | Executed → Terminated | DNS Resolution Delay Removed |
| Inline JS Execution | Executed → Terminated | Main Thread Execution Saved |
| External SVG Payload | Executed per Emoji → Terminated (Native Font) | HTTP Request Eliminated |
Modification 6: Cryptographic Containment of Scalable Vector Graphics (SVG) Uploads
Scalable Vector Graphics (SVG) represent the absolute industry standard for high-fidelity, resolution-independent digital imagery across the modern web.
Characterized by exceptionally small file sizes and mathematically perfect scaling capabilities, SVGs are strictly required for modern corporate logo deployment, complex iconography systems, and advanced CSS animation routines.
However, the native WordPress media library explicitly prohibits the upload of SVG files, citing profound security vulnerabilities inherent to the file structure.
Unlike rasterized image formats such as JPEG, WebP, or PNG, which map static hex color values to a predefined pixel grid, an SVG is fundamentally an XML text document. Browsers do not merely process SVGs as flat images; they parse the underlying XML markup language through their layout engines. This parsing mechanism introduces a massive vector for cybersecurity exploitation.
A malicious actor can easily craft an SVG file containing embedded, executable JavaScript payloads enclosed within <script> tags, or reference malicious external entities via XML External Entity (XXE) configurations.
If a compromised SVG is successfully uploaded to a web server and subsequently rendered in a victim's browser, the embedded JavaScript will execute seamlessly within the trusted security context of the host domain.
This facilitates devastating Cross-Site Scripting (XSS) attacks, allowing adversaries to hijack highly privileged session cookies, orchestrate unauthorized administrative database actions, or deploy brute-force network amplifications.
Because automated sanitization algorithms struggle to guarantee the mathematical elimination of all obfuscated XML payloads, the safest architectural approach is to selectively permit the .svg Multipurpose Internet Mail Extensions (MIME) type while strictly binding the permission to the highest-level cryptographic roles.
function restrict_svg_uploads_to_administrators( $mimes ) {
if ( current_user_can( 'manage_options' ) ) {
$mimes['svg'] = 'image/svg+xml';
}
return $mimes;
}
add_filter( 'upload_mimes', 'restrict_svg_uploads_to_administrators' );This strategic implementation intercepts the upload_mimes filter, which defines the global array of permissible file extensions. Crucially, the assignment logic is wrapped in a strict validation check utilizing current_user_can( 'manage_options' ). This completely isolates the upload capability strictly to users holding the 'Administrator' role.
By categorically denying lower-privileged users (such as Authors or external Contributors) the computational ability to manipulate XML documents, the attack surface is mathematically contained. It is highly advised that organizations only source raw SVG files from strictly vetted, internal design teams to minimize inherent risk.
Modification 7: Overriding Server Environment Limits for Heavy Payload Uploads
The capability to upload high-fidelity assets, massive database backups, or complex architectural plugins is heavily regulated by underlying PHP environmental configurations.
By default, many shared hosting providers and default PHP installations impose extremely restrictive caps on data processing limits, frequently setting the maximum permissible upload size as low as 2 megabytes.
This restriction exists primarily as a baseline defense against external resource exhaustion attacks, where an adversary attempts to flood the server by submitting terabytes of continuous dummy data to a processing script.
However, in professional enterprise environments, a 2MB ceiling is completely non-viable. Modern web deployment frequently requires the uploading of uncompressed high-resolution WebP hero graphics, heavy video backgrounds, or bulk data imports via CSV formats.
Attempting to bypass these constraints via heavy third-party plugins is inefficient, as the application layer ultimately must request permission from the PHP engine. Engineers bypass these constraints by executing targeted overrides during the early initialization phase of the PHP lifecycle.
@ini_set( 'upload_max_size', '64M' );
@ini_set( 'post_max_size', '64M');
@ini_set( 'max_execution_time', '300' );This specific code snippet, typically deployed within a system's core configuration files or managed snippet environment, directly interfaces with the core php.ini directives. It utilizes the @ini_set construct to suppress potential warning outputs while simultaneously redefining three critical variables.
First, it escalates the upload_max_size to 64 megabytes, permitting large single-file transfers. Second, it elevates the post_max_size to match, ensuring that the total HTTP POST payload containing the file and associated metadata is not prematurely rejected by the server.
Finally, it significantly increases the max_execution_time to 300 seconds. This crucial third step guarantees that the PHP worker is granted sufficient temporal latitude to process, scan, and allocate the 64 megabyte file into the destination directory before the server triggers a fatal timeout exception.
| Override Mechanism (Scope) | Server Compatibility | Implementation Difficulty |
|---|---|---|
| functions.php / Snippet (Application Layer) |
High (If ini_set is permitted) |
Low |
| .htaccess (php_value) (Directory / Subdirectory) |
Apache Only | Medium |
| .user.ini file (Root Directory) |
Nginx / FastCGI Servers | Medium |
Modification 8: Obfuscating Core Telemetry to Thwart Automated Reconnaissance
The initial phase of any sophisticated cyberattack or systemic breach is reconnaissance. Adversaries utilize distributed, automated botnets to crawl the public internet, relentlessly analyzing HTTP header responses and DOM structures to catalog the underlying software architectures of millions of distinct websites.
When a zero-day vulnerability or critical Common Vulnerabilities and Exposures (CVE) identifier is publicly disclosed for a specific version of a CMS or third-party plugin, the botnet operators immediately query their vast databases to deploy targeted exploit payloads against all known vulnerable targets.
By default, the WordPress rendering engine operates with profound operational transparency, aggressively broadcasting its exact core version number to the public via a meta tag injected directly into the HTML <head> section, typically formatted as <meta name="generator" content="WordPress X.X.X">.
Furthermore, these version strings are frequently appended to the end of static CSS and JavaScript URLs as query parameters (e.g., style.css?ver=X.X.X) to force browser cache invalidation upon updates.
This systemic information disclosure provides hostile actors with a highly deterministic, readily available map of the application's structural vulnerabilities. Neutralizing this passive broadcast telemetry requires programmatic intervention during the DOM assembly phase to intercept the logic before it writes to the output buffer.
remove_action('wp_head', 'wp_generator');
remove_action('wp_head', 'rsd_link');
remove_action('wp_head', 'wlwmanifest_link');
remove_action('wp_head', 'wp_shortlink_wp_head');
remove_action('wp_head', 'rest_output_link_wp_head');This block of code executes a precise series of remove_action directives. It intercepts the wp_head hook and systematically unbinds the wp_generator function, effectively severing the application's ability to print its primary version number into the HTML markup.
To further obfuscate the underlying infrastructure and trim the DOM payload size, this script also strips other legacy meta tags that reveal application architecture, such as Really Simple Discovery (RSD) endpoint links, Windows Live Writer (WLW) manifests, and raw REST API discovery links.
By systematically executing these removals, the frontend structural output becomes highly opaque. While security through obscurity is never a primary or standalone defensive posture, applying this code mathematically reduces the probability of falling victim to automated, broad-spectrum vulnerability scanning and opportunistic exploit deployment routines.
Modification 9: Hardening Internal Infrastructure via Administrative Editor Neutralization
The cybersecurity principle of least privilege dictates that a system should grant users only the permissions fundamentally required to perform their designated operational tasks.
Within the default WordPress architecture, users possessing administrative rights are granted access to a native graphical interface located at Appearance > Theme File Editor and Plugins > Plugin File Editor. This interface permits the direct reading, modification, and execution of the raw PHP files governing the application directly from the web browser.
While convenient for rapid, on-the-fly development, this feature presents a catastrophic security vulnerability in production environments. In the event that an administrator's credentials are compromised - via sophisticated phishing campaigns, brute force attacks, or session token hijacking - the attacker does not need to deploy complex remote code execution (RCE) exploits to gain total system control.
Instead, the adversary can simply utilize the native file editor to inject an obfuscated PHP webshell or persistent backdoor directly into the active theme's functions.php file.
Because the core application explicitly facilitates and authorizes this modification, network-level intrusion detection systems (IDS) and external web application firewalls (WAF) frequently fail to flag the behavior as anomalous. This methodology is known in cybersecurity circles as "living off the land."
To permanently eliminate this internal vulnerability, engineers must define strict immutable constants within the core wp-config.php file, thereby irrevocably altering the application's foundational initialization parameters.
define('DISALLOW_FILE_EDIT', true);By setting DISALLOW_FILE_EDIT to true, the application completely strips the theme and plugin editors from the administrative interface and mathematically blocks all internal API requests attempting to execute source code modifications.
For maximum security, particularly in highly regulated enterprise deployments where system stability supersedes administrative convenience, this directive can be escalated to its absolute maximum constraint.
define('DISALLOW_FILE_MODS', true);The DISALLOW_FILE_MODS constant is the ultimate infrastructure lockdown mechanism. It inherits all the restrictions of disabling the file editor, but aggressively extends the protocol to completely block the installation, deletion, or updating of any plugins or themes from within the dashboard entirely.
Once defined, all cryptographic and infrastructural changes must be executed via secured Secure Shell (SSH) connections, SFTP, or automated continuous integration/continuous deployment (CI/CD) pipelines, isolating the application layer entirely from the underlying physical file system.
Modification 10: Dynamic Excerpt Truncation for Frontend Content Layouts
In complex enterprise environments focusing on digital publishing and highly structured frontend grid designs, maintaining visual symmetry across user interfaces is paramount.
By default, the core application handles post excerpts by pulling a predefined number of words from the primary content block. If no manual excerpt is defined, the system automatically truncates the content.
However, the default truncation parameters frequently result in jagged, uneven masonry grids on the frontend, causing cumulative layout shifts (CLS) and degrading the visual aesthetic.
Furthermore, relying on heavy visual builder plugins to manipulate this data output introduces unnecessary logic processing at the rendering layer. Engineers solve this by intervening at the data retrieval phase using the excerpt_length hook.
function custom_enterprise_excerpt_length( $length ) {
return 30;
}
add_filter( 'excerpt_length', 'custom_enterprise_excerpt_length', 999 );
This fundamental approach intercepts the core loop and forces a strict integer return (e.g., 30 words), utilizing a high priority (999) to ensure it overrides any conflicting theme behaviors.
For advanced grid architectures requiring extreme precision, engineers frequently deploy highly complex string manipulation logic to dynamically alter the excerpt based on the exact character count of the associated post title, ensuring absolute geometric symmetry within the DOM block.
function advanced_dynamic_excerpt_length() {
global $post;
$title_len = strlen($post->post_title);
$rem_len = 188;
if($title_len <= 35) { $rem_len = 188; }
elseif($title_len <= 70) { $rem_len = 146; }
elseif($title_len <= 105) { $rem_len = 104; }
$trunc_ex = substr($post->post_excerpt, 0, $rem_len);
if(strlen($trunc_ex) < strlen($post->post_excerpt)) {
$trunc_ex = $trunc_ex . " [...] <a href='" . get_permalink($post->ID) . "'>Read more</a>";
}
echo "<p>" . $trunc_ex . "</p>";
}This advanced execution logic retrieves the global $post object and utilizes standard PHP strlen functions to calculate the exact spatial requirements of the typography. By dynamically resizing the excerpt string based on title length and programmatically appending the hyperlinked "Read more" tag directly into the output array, the system guarantees perfect block alignment without relying on heavy frontend CSS or JavaScript recalculations.
| Truncation Methodology | Execution Context | Consistency & Overhead |
|---|---|---|
| excerpt_length Hook | Standard Word Count | Medium Consistency (Varies by word size); Extremely Low Overhead |
| substr Character Limiting | Strict Character Count | High Consistency (Predictable sizing); Low Overhead |
| Dynamic Title/Body Math | Algorithmic Computation | Perfect Consistency (Geometric symmetry); Medium Overhead |
Abstract Deployment Architectures and Serverless Evolution
The deployment of the aforementioned architectural modifications requires rigorous, error-free execution protocols. Historically, the standard industry procedure involved pasting raw PHP logic into a child theme's functions.php file.
While functionally viable, this legacy approach inextricably binds highly critical operational logic to the visual presentation layer. If an organization executes a theme migration or restructuring, all custom security protocols, optimization parameters, and interface modifications are instantaneously lost, potentially exposing the system to catastrophic failure.
To completely decouple core execution logic from aesthetic themes, enterprise environments have rapidly transitioned to utilizing abstract logic managers, commonly referred to as advanced code management systems or snippet processors (e.g., WPCode, Code Snippets). These dedicated platforms process PHP, CSS, and JavaScript from an organized, database-driven virtual dashboard.
These systems introduce vital safety paradigms previously absent from the core. Advanced managers execute "smart code validation" by analyzing the Abstract Syntax Tree (AST) of the PHP prior to committing the logic to the database.
If a systems engineer introduces a fatal syntax error - such as a missing semicolon, an unclosed bracket, or a conflicting function name - the logic manager preemptively halts execution, mathematically preventing a critical parse error that would otherwise result in a complete application crash and total system lockout.
Furthermore, these platforms allow for deep conditional logic execution matrices; for instance, ensuring that a specific JavaScript unhook operation fires exclusively on specific checkout nodes, bypassing the rest of the application ecosystem entirely to conserve execution memory.
Looking toward the ultimate evolutionary trajectory of the CMS ecosystem, the entire concept of internal PHP code execution is actively being re-evaluated at the infrastructural level.
Experimental, high-performance open-source projects - such as EmDash, designed as a spiritual, fully TypeScript-based successor to legacy WordPress - seek to completely resolve the fundamental security flaws of the internal functional architecture by abandoning the PHP monolith entirely.
By operating entirely within a distributed, edge-based serverless ecosystem (such as Cloudflare Dynamic Workers utilizing the Astro web framework), next-generation logic does not share the same memory space as the core application database.
Functions, modifications, and routing overrides are executed in strictly sandboxed, distributed V8 isolates globally. In these futuristic paradigms, the necessity for deeply embedded overrides (such as disabling the native file editor) is entirely bypassed by the nature of the serverless hardware topology, which dynamically scales and intrinsically denies local file system modifications by design.
Until such serverless methodologies achieve total market saturation, rigorous, abstract manipulation of the execution lifecycle remains the absolute standard for CMS engineering.
Synthesized Conclusions on Core Architectural Optimization
The profound transformation of a default content management installation into a hardened, hyper-optimized enterprise architecture demands an absolute, uncompromising commitment to code efficiency.
The data demonstrates unequivocally that reliance on multifaceted software packages to achieve discrete, singular modifications introduces mathematically unacceptable levels of computational latency, relational database bloat, and cryptographic vulnerability.
By systematically applying raw, programmatic directives - disabling outdated remote procedural protocols, throttling asynchronous client-server polling mechanisms, enforcing strict boundaries on relational database sprawl, stripping render-blocking stylesheets from the critical rendering path, circumventing legacy telemetry networks, scaling backend environmental constraints, and isolating the application from physical file modifications - engineers succeed in stripping away the vast majority of systemic liabilities inherent to the default state.
This rigorous methodology ensures that the underlying computational velocity provided by modern server infrastructure is fully transferred to the end-user without latency interception.
Ultimately, prioritizing surgical code intervention over third-party software bloat is the foundational prerequisite for maintaining digital supremacy, ensuring maximum data throughput, and cultivating an impenetrable defensive network posture in an increasingly hostile, automated web ecosystem.
Senior Software Architect & Open‑Source Maintainer
Dr. Marcus Hale holds a PhD in Computer Science from Carnegie Mellon University. He specializes in curating secure, production‑ready code snippets and software architecture best practices.